The Truth Every Indian Needs to Know About Aadhaar Security
Introduction: The Fear Every Indian Has Felt
You’ve probably heard this somewhere:
“Don’t share your Aadhaar number — someone can hack you.”
Or maybe:
“If someone gets your Aadhaar, they can empty your bank account.”
These statements spread fast on WhatsApp, reels, and even news debates. And honestly, they sound believable.
After all, Aadhaar is linked to:
- Your bank accounts
- Mobile SIM
- PAN card
- Government benefits
- KYC for services
So the question naturally arises:
Can someone hack you just by knowing your Aadhaar number?
The answer is not as simple as “yes” or “no”.
This article will break down:
- What Aadhaar actually is
- What someone can and cannot do with your Aadhaar number
- Real-world scams and misuse cases in India
- How hackers actually exploit Aadhaar
- How to protect yourself
No fear-mongering. No oversimplification. Just facts.
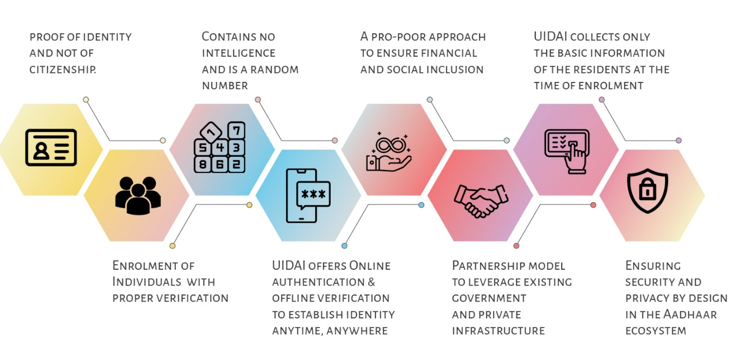
🧾 What Is Aadhaar and How Does It Work?
Aadhaar is a 12-digit unique identity number issued by
Unique Identification Authority of India (UIDAI).
It is based on:
- Biometric data (fingerprints, iris scan)
- Demographic data (name, DOB, address)
It is designed to:
- Verify identity
- Enable direct benefit transfers
- Simplify KYC processes
Unlike passwords, Aadhaar is not secret — it’s an identifier.
That’s a crucial point many people misunderstand.
🔐 Aadhaar Number vs Aadhaar Authentication
Let’s clear the biggest confusion.
❗ Aadhaar Number Alone ≠ Access
Just knowing your Aadhaar number does NOT allow someone to:
- Withdraw money
- Access your bank account
- Clone your identity instantly
To use Aadhaar for authentication, additional layers are required:
- OTP (sent to your registered mobile)
- Biometrics (fingerprint/iris)
- Sometimes face authentication
Think of Aadhaar like your username, not your password.
🚨 So… Can Someone Hack You Using Aadhaar Number?
🟢 Short Answer:
No — Aadhaar number alone cannot hack you.
🔴 But…
It can be used as a starting point for scams.
That’s where things get dangerous.
🧠 How Aadhaar Is Actually Misused in Real Life
Let’s move from theory to reality.
1️⃣ SIM Swap Fraud Using Aadhaar
How it works:
- Attacker gets your Aadhaar number + basic details
- Uses fake ID or social engineering at telecom store
- Requests SIM replacement
- Gains control of your mobile number
- Intercepts OTPs
- Accesses bank accounts
👉 Aadhaar alone is not enough — but combined with weak verification, it becomes dangerous.
2️⃣ Fake KYC Scams
You may receive calls like:
“Sir, your bank KYC is incomplete. Please share Aadhaar and OTP.”
What happens:
- You share Aadhaar + OTP
- Scammer completes eKYC
- Gains access to financial services
3️⃣ Loan Fraud Using Aadhaar
Real Case Example (India)
Many victims reported:
- Instant loan apps issued loans in their name
- They never applied
- Recovery agents started harassment
How?
- Aadhaar + PAN + phone number
- Fake KYC + weak app verification
4️⃣ Aadhaar Data Leaks
There have been multiple reports of:
- Government portals exposing Aadhaar-linked data
- Misconfigured databases
- Third-party vendor leaks
Even if Aadhaar database itself is secure, ecosystem leaks are a risk.
📊 What Can Someone Do With Your Aadhaar Number?
| Action | Possible? | Explanation |
|---|---|---|
| Withdraw money directly | ❌ No | Needs OTP/biometric |
| Open bank account | ⚠️ Sometimes | With fake KYC |
| Get SIM card | ⚠️ Possible | If telecom verification is weak |
| Apply for loan | ⚠️ Possible | Through shady apps |
| Track your location | ❌ No | Aadhaar doesn’t provide tracking |
| Access Aadhaar database | ❌ No | Highly secured by UIDAI |
🔍 Real Threat: Aadhaar + Social Engineering
Cybercrime in India is not about hacking systems.
It’s about hacking people.
Most scams involve:
- Fear (“Your account will be blocked”)
- Urgency (“Do it now”)
- Authority (“I am calling from bank”)
Aadhaar is used as:
- Trust-building tool
- Identity anchor
Not as a hacking tool.
🧨 Example Scenario
Let’s say a scammer has:
- Your Aadhaar number
- Your phone number
They call you:
“Your Aadhaar is linked to suspicious activity. Verify immediately.”
You panic.
You share OTP.
Game over.
👉 The breach didn’t happen because of Aadhaar.
👉 It happened because of manipulation.
🏛️ Security Measures by UIDAI


UIDAI provides several protections:
✅ Virtual ID (VID)
- Temporary Aadhaar replacement
- Can be regenerated anytime
✅ Masked Aadhaar
- Shows only last 4 digits
- Safe for sharing
✅ Biometric Lock
- Prevents fingerprint misuse
✅ Aadhaar Authentication History
- Track usage
✅ OTP-based verification
These tools are underused by most Indians.
🛡️ How to Protect Yourself (Practical Guide)
🔒 1. Lock Your Biometrics
Use UIDAI portal or mAadhaar app.
🔑 2. Use Virtual ID Instead of Aadhaar
Never share full Aadhaar unless absolutely necessary.
📵 3. Never Share OTP
No bank or government agency will ask for OTP.
📞 4. Avoid Unknown Calls
Especially:
- KYC update calls
- Loan offers
- “Police verification” scams
📄 5. Use Masked Aadhaar
Download from UIDAI website.
🔍 6. Check Authentication History
Regularly monitor activity.
📱 7. Secure Your SIM
- Add SIM lock
- Enable alerts
⚖️ Legal Perspective in India
Aadhaar misuse falls under:
- IT Act, 2000
- Aadhaar Act
- IPC sections for fraud
Unauthorized use is punishable.
But again:
Having your Aadhaar number ≠ committing fraud.
📈 Why This Fear Is Growing in India
Because:
- Aadhaar is linked everywhere
- Digital adoption is massive
- Awareness is low
- Scams are increasing
Fear fills the gap where knowledge is missing.
🧠 Final Truth
Let’s simplify everything:
👉 Aadhaar number alone cannot hack you
👉 Aadhaar is an ID, not a password
👉 Real risk = social engineering + weak systems
👉 Awareness > fear
🎯 Conclusion: Stay Smart, Not Scared
India is rapidly digitizing.
Aadhaar plays a central role in that transformation.
Yes, risks exist.
But they are not what viral content makes them seem.
You are not vulnerable because someone knows your Aadhaar number.
You are vulnerable if:
- You trust blindly
- You share OTP
- You ignore security practices
Cybersecurity is not about hiding your identity — it’s about controlling access.
📣 Call to Action
If this article helped you:
- Share it with family (especially parents)
- Educate at least one person about OTP scams
- Take 5 minutes today to lock your Aadhaar biometrics
Because awareness is the strongest firewall.
❓ FAQ
Can someone hack my bank account with Aadhaar number?
No. Aadhaar alone is not enough. OTP or biometric authentication is required.
Is it safe to share Aadhaar number?
It depends. Avoid sharing full Aadhaar. Use masked Aadhaar or Virtual ID.
Can someone take a loan using my Aadhaar?
Yes, in some cases through weak verification systems or fake KYC. Always monitor your financial activity.
What should I do if my Aadhaar is misused?
- Report to UIDAI
- File complaint at cybercrime.gov.in
- Inform your bank
Can Aadhaar track my location?
No. Aadhaar does not have GPS or tracking capability.
Is Aadhaar database hacked?
There is no confirmed large-scale breach of UIDAI core database, but ecosystem leaks have occurred.

