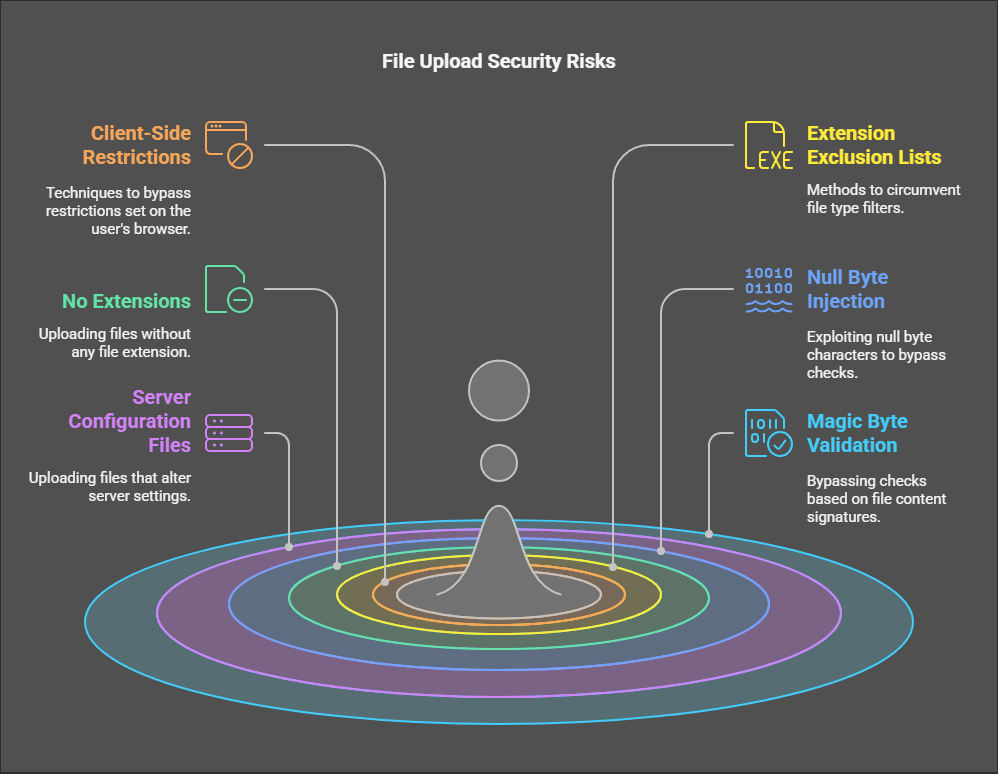
File upload functionality is a common feature in web applications, but it also introduces severe security risks if not implemented correctly. Attackers often exploit weak validation mechanisms to upload malicious files, gain unauthorized access, or execute arbitrary code on a server. This article explores various techniques to bypass file upload restrictions and provides insights into securing web applications against such attacks.
1. Checking for Client-Side Restrictions
Many web applications implement file upload restrictions using JavaScript or HTML5 attributes, such as:
- Accepting specific file types (
accept="image/*") - Limiting file size (
max-sizeattributes) - Restricting extensions using JavaScript validation
Bypassing Client-Side Restrictions
Since client-side checks can be easily bypassed, attackers use tools like:
- Burp Suite/ZAP Proxy – Intercept and modify HTTP requests before reaching the server.
- DevTools (F12 in browsers) – Modify HTML/JavaScript restrictions and remove file validation rules.
- Custom scripts with cURL/Python – Directly send requests without relying on the web interface.
Prevention
Client-side validation should only be used to enhance user experience. Proper validation must be enforced server-side to prevent unauthorized file uploads.
2. Bypassing File Extension Exclusion Lists
Many applications restrict file uploads based on their extensions, commonly blocking .php, .exe, .js, and other executable formats. However, attackers bypass such rules using alternative techniques:
Techniques for Bypassing Extension Filters
- Using Alternative Extensions:
- Some servers recognize other extensions as PHP code execution points:
file.phtml, file.php7, file.phar, file.inc - If
.phpis blocked, renaming to.phtmlmight still work.
- Some servers recognize other extensions as PHP code execution points:
- Double Extensions:
- Uploading files like
shell.php.jpg,image.png.php, ortest.asp;.jpg - Some misconfigured servers execute code if the second extension is executable.
- Uploading files like
- MIME-Type Mismatch:
- If the server only checks MIME type, renaming a PHP file to
.pngbut keeping its content unchanged might lead to execution.
- If the server only checks MIME type, renaming a PHP file to
Prevention
- Implement strict server-side extension filtering.
- Use MIME type verification to ensure only legitimate file formats are processed.
- Store uploaded files outside the web root and serve them using secure methods (e.g., generating a random filename and providing download access through a controlled API).
3. Uploading Files with No Extensions
Some applications allow file uploads but rely solely on extensions for validation. If a user uploads malware.exe, it is blocked, but malware (without an extension) may still be accepted.
Exploitation
- Some web servers infer the file type from its content and execute it accordingly.
- If an attacker can later rename or execute the file, they may achieve remote code execution (RCE).
Prevention
- Require specific extensions for all uploaded files.
- Do not rely on filenames alone—validate file contents and metadata before processing.
4. Null Byte Injection (%00 Null Byte Trick)
What is a Null Byte Injection?
A null byte (\x00 or %00 in URLs) is often used to prematurely terminate string processing in poorly coded applications.
How Attackers Use It
- If a server checks for
.pngat the end of a filename but stops at a null byte, attackers can upload a file like:shell.php%00.png- The validation might read it as
.png, but the actual file remains.phpand can be executed.
- The validation might read it as
Prevention
- Use proper string-handling functions that are null-byte safe.
- Avoid depending solely on string matching for validation.
5. Uploading Server Configuration Files
Attackers often attempt to upload files like:
.htaccess(Apache)web.config(IIS)
These files can be used to override server configurations and enable dangerous functionalities like:
- Enabling execution of uploaded PHP files.
- Changing MIME types to allow execution.
Example: .htaccess Exploit
AddType application/x-httpd-php .jpg
- This forces the server to execute
.jpgfiles as PHP scripts, allowing an attacker to uploadshell.jpgcontaining PHP code.
Prevention
- Deny uploads of
.htaccessand similar files. - Set proper permissions to restrict user modifications to server configuration files.
6. Bypassing Magic Byte Validation
Many applications check file contents instead of extensions by inspecting magic bytes (signature identifiers at the beginning of a file).
Common File Signatures
- PNG:
89 50 4E 47 0D 0A 1A 0A - JPG:
FF D8 FF - PDF:
%PDF-
Bypassing Magic Byte Checks
Attackers can modify the header of a PHP file to appear as an image:
printf "\x89\x50\x4E\x47\x0D\x0A\x1A\x0A<?php system(\$_GET['cmd']); ?>" > shell.png
- This tricks the server into recognizing the file as a PNG while still allowing PHP execution.
Prevention
- Perform deep content inspection instead of relying on the first few bytes.
- Convert all uploaded images into a new file format before saving.
Additional Techniques for File Upload Exploitation
7. Overwriting Existing Files
- If the upload directory allows overwriting, an attacker can replace an existing script file and execute arbitrary code.
8. Race Conditions in Upload Handling
- If a system first checks a file and then processes it asynchronously, an attacker might swap the file before execution.
9. Symlink Attacks
- If symbolic links are allowed, attackers can create links to sensitive files (e.g.,
/etc/passwd) and attempt to access them.
10. Using Image Metadata for Code Execution
- Some PHP servers allow execution of code inside EXIF metadata in images:
<?php system($_GET['cmd']); ?>- If an application extracts EXIF data without sanitization, this can lead to RCE.
Defending Against File Upload Attacks
1. Server-Side Validation is Critical
- Enforce strict extension whitelisting.
- Verify file content and MIME type.
- Store uploads outside the web root and serve them securely.
2. Rename and Randomize Uploaded Files
- Do not retain user-provided filenames.
- Use UUIDs or hashes to prevent overwriting and guessing.
3. Set Proper Permissions
- Uploaded files should never have execute permissions.
- Restrict the web server from executing files in the upload directory.
4. Convert Files to Safe Formats
- If allowing image uploads, convert them to a secure format using tools like ImageMagick.
5. Monitor and Audit File Uploads
- Log and monitor file upload activity for anomalies.
- Use intrusion detection systems to detect suspicious behavior.
Conclusion
File upload vulnerabilities are a serious risk to web applications. Attackers continuously find new ways to bypass security restrictions and execute arbitrary code on the server. Developers must implement strict validation, server-side security controls, and monitoring to prevent exploitation. By following best practices, organizations can ensure that file uploads remain a useful feature without becoming a security nightmare.
Discover more from Spyboy blog
Subscribe to get the latest posts sent to your email.

