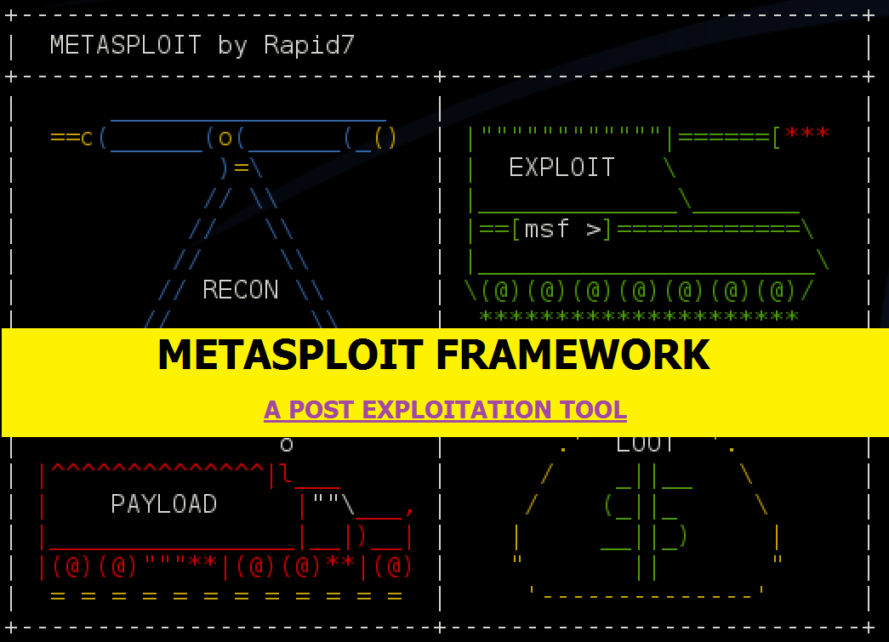
The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in penetration testing and IDS signature development. Metasploit is a tool which is used by penetration testers and security experts for post-exploitation.

With the help of this tool, you can hack any Windows/Linux Operating System, it has inbuilt payloads and exploits which you can also update by following command i.e. msfupdate.

Metasploit interfaces –
There are several interfaces for Metasploit available. The most popular are maintained by Rapid7 and Strategic Cyber LLC.
1) Metasploit Framework Edition
The free version. It contains a command-line interface, third-party import, manual exploitation and manual brute-forcing.
2) Metasploit Community Edition
In October 2011, Rapid7 released Metasploit Community Edition, a free, web-based user interface for Metasploit. Metasploit Community is based on the commercial functionality of the paid-for editions with a reduced set of features, including network discovery, module browsing and manual exploitation. Metasploit Community is included in the main installer.
3) Metasploit Express
In April 2010, Rapid7 released Metasploit Express, an open-core commercial edition for security teams who need to verify vulnerabilities. It offers a graphical user interface, integrates nmap for discovery, and adds smart bruteforcing as well as automated evidence collection.
4) Metasploit Pro
In October 2010, Rapid7 added Metasploit Pro, an open-core commercial Metasploit edition for penetration testers. Metasploit Pro adds onto Metasploit Express with features such as Quick Start Wizards/MetaModules, building and managing social engineering campaigns, web application testing, an advanced Pro Console, dynamic payloads for anti-virus evasion, integration with Nexpose for ad-hoc vulnerability scans, and VPN pivoting.
5) Armitage
Armitage is a graphical cyber attack management tool for the Metasploit Project that visualizes targets and recommends exploits. It is a free and open-source network security tool notable for its contributions to red team collaboration allowing for shared sessions, data, and communication through a single Metasploit instance.
6) Cobalt Strike
Cobalt Strike is a collection of threat emulation tools provided by Strategic Cyber LLC to work with the Metasploit Framework. Cobalt Strike includes all features of Armitage and adds post-exploitation tools, in addition, to report generation features.
HOW TO USE METASPLOIT?
First of all, start the metasploit service
Command:
applications > kali linux > system services > metasploit > start
or
service metasploit start
Run msfconsole
just type msfconsole in your terminal
Command:
sudo msfconsole
What is msfconsole?
Msfconsole is the main interface to metasploit. There are GUI interfaces (armitage), and a web interface too (websploit). With msfconsole, you can launch exploits, create listeners, configure payloads etc.
Metasploit has lots of great documentation built in. Type help to get a basic list of commands, like if you want to check what commands you can use then just type help or ? <- question mark
Example::
msf > help
Core Commands
=============Command Description
————- ————–
- ? Help menu
- advanced Displays advanced options for one or more modules
- back Move back from the current context
- banner Display an awesome metasploit banner
- cd Change the current working directory
- color Toggle color
- connect Communicate with a host
- edit Edit the current module with $VISUAL or $EDITOR
- exit Exit the console
- get Gets the value of a context-specific variable
- getg Gets the value of a global variable
- grep Grep the output of another command
- help Help menu
- info Displays information about one or more modules
- irb Drop into irb scripting mode
- jobs Displays and manages jobs
- kill Kill a job
- load Load a framework plugin
- loadpath Searches for and loads modules from a path
- makerc Save commands entered since start to a file
- options Displays global options or for one or more modules
- pushm Pushes the active or list of modules onto the module stack
- quit Exit the console
- reload_all Reloads all modules from all defined module paths
- rename_job Rename a job
- resource Run the commands stored in a file
- route Route traffic through a session
- save Saves the active datastores
- search Searches module names and descriptions
- sessions Dump session listings and display information about sessions
- set Sets a context-specific variable to a value
- setg Sets a global variable to a value
- show Displays modules of a given type, or all modules
- sleep Do nothing for the specified number of seconds
- spool Write console output into a file as well the screen
- threads View and manipulate background threads
- unload Unload a framework plugin
- unset Unsets one or more context-specific variables
- unsetg Unsets one or more global variables
- use Selects a module by name
- version Show the framework and console library version numbers
Database Backend Commands
=========================Command Description
————- ————–
- creds List all credentials in the database
- db_connect Connect to an existing database
- db_disconnect Disconnect from the current database instance
- db_export Export a file containing the contents of the database
- db_nmap Executes nmap and records the output automatically
- db_rebuild_cache Rebuilds the database-stored module cache
- db_status Show the current database status
- hosts List all hosts in the database
- loot List all loot in the database
- notes List all notes in the database
- services List all services in the database
- vulns List all vulnerabilities in the database
- workspace Switch between database workspaces
msf >
Pick a vulnerability and use an exploit
Once you know what your remote hosts system is (nmap, lynix, maltego, wp-scan, etc) you can pick an exploit from Metasploit to test. rapid7 have an easy way to find exploits.
There is also a way to search within msfconsole for various exploits:
Example:
- search type:exploit
- search name:xxxx
- search CVE-xxx-xxx
- search cve:2016

Posted by Shubham ;)


